In the digital age, data security is universally accepted as a major consideration when adopting new technologies.
Businesses and agencies involved in the collection of remote environmental monitoring data are no exception. Globally there are hundreds of thousands of monitoring devices recording and transmitting weather and environmental data daily. These data streams are vulnerable to malicious behavior in much the same way that we experience with our bank and email accounts. Real world examples include manipulation of weather data to change fire risk codes and the hacking of private digital networks for bit torrent streaming. No business or agency wants to experience their systems and data abused in this manner. Because of these concerns, FTS has incorporated end-to-end 256-bit AES data encryption, security protocols and standards into all facets of our FTS360 SaaS platform from data collection, transmission, visualization and ultimately data storage in our secure cloud databases.
At the data collection edge, individual devices have distinctive encrypted credentials.
“With cellular-based systems, each station is given its own set of FTS360 credentials to connect to the broker,” says Sean Daniel, FTS Software Manager. “This ensures that the data we’re getting from a specific station is really the data from that station, because it has logged in and provided its own set of credentials. We can also reset or remove those credentials and block specific stations out of the system.”
Whether transmitting via GOES, cellular, or Iridium, a secure funnel is provided to ensure that the data received is that which was sent without delay or alteration.
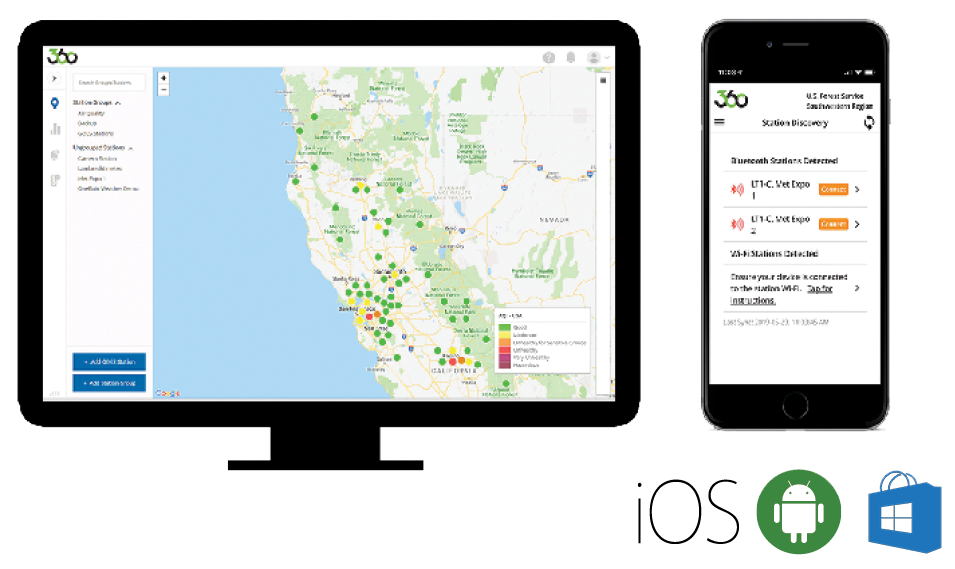
“At the highest level FTS360 is a data and imagery collection, distribution, and visualization platform,” explains Daniel. “It’s an always-available cloud-based software-as-a-service platform that accepts data and imagery from remote stations and cameras in the field over various telemetry types, and then stores the data in a secure online database so the owners of those stations can easily view, access, and distribute. It also allows users to adjust network configurations and respond to changing conditions without leaving the office.”
In order to access FTS360 a user must have an active account. This can only be obtained by an invitation from an agency administrator.
“FTS360 uses a token-based system,” states Daniel. “When a user first logs in, they supply us with a password for authentication. We then encrypt the password and return a token that they use to access the system. It makes it harder for hackers to hack and get access to a user’s password, because the password is only sent once. And if a user doesn’t access the system for a period of time, their token expires and they are forced to re-log in. We also invalidate tokens and re-issue new tokens as needed.” An administrator can just as easily deactivate a user’s account. Because all passwords are hidden from view, this person is now locked out from obtaining data or performing a malicious deed.
FTS understands how important data security is, especially when servicing government offices. It is because of our dedication to security that we’ve built our system ground up with layers of protection, ultimately resulting in FTS360 being adopted by agencies worldwide and trusted as a visualization platform during the most extreme weather events.
Look for the next post on FTS360, where we will examine its adoption of MQTT (message queuing telemetry transport) and the value it brings. In the meantime, if you have questions about FTS360 contact us.